How Do Digital Assets Self-Custody? OpenAI Cofounder's 15-Step Checklist
Original Title: How to stay digitally secure in the Age of Claude Mythos (using Karpathy's 15-step checklist)
Original Author: Ole Lehmann
Translation: Peggy, BlockBeats
Editor's Note: As AI capabilities begin to approach the boundary of a "general tool," the meaning of cybersecurity is also changing. It is no longer just a defense issue against hackers, viruses, or data breaches but is evolving into a game of "asymmetric capabilities."
With Anthropic's introduction of Claude Mythos showcasing top-level expert-like vulnerability discovery, network attacks are entering a more covert and automated new stage, and individual security is transitioning from being an "option" to a "necessity." On one hand, the attack threshold is being lowered, and on the other hand, attack efficiency is exponentially increasing. This means that "passive security" will become increasingly unsustainable.
In this context, OpenAI co-founder Andrej Karpathy's proposed "digital hygiene" checklist offers an actionable response path. In the AI era, security is no longer just a "remedy after an incident" but part of "daily behavior." Identity verification, permission isolation, information minimization, and habit reformation. The seemingly trivial 15 steps essentially reconstruct a security boundary that an ordinary user can control.
The true risk lies not in whether you are a target of an attack but in whether you are defenseless when an attack occurs.
The following is the original text:
What can be certain is that when it comes to cybersecurity, you no longer have room to be lazy.
The milestone Mythos released by Anthropic yesterday marks a point of no return.

This technology is not yet public, but once it falls into the hands of malicious actors (which is almost inevitable)... you will face an extremely advanced cyberattack, with most people realizing it is too late even before they are aware they have been breached.
It's like the "COVID-19 of the software world."
It is for this reason that from now on, your cybersecurity must be watertight.
Karpathy's Digital Hygiene Guide
Last year, Andrej Karpathy (@karpathy, Co-Founder of OpenAI) compiled a "Digital Hygiene Guide," systematically outlining foundational methods to protect oneself in the AI era.
This is one of the most worthwhile introductory guides I've come across.
Here are all the security measures you should take in this era of uncertainty:
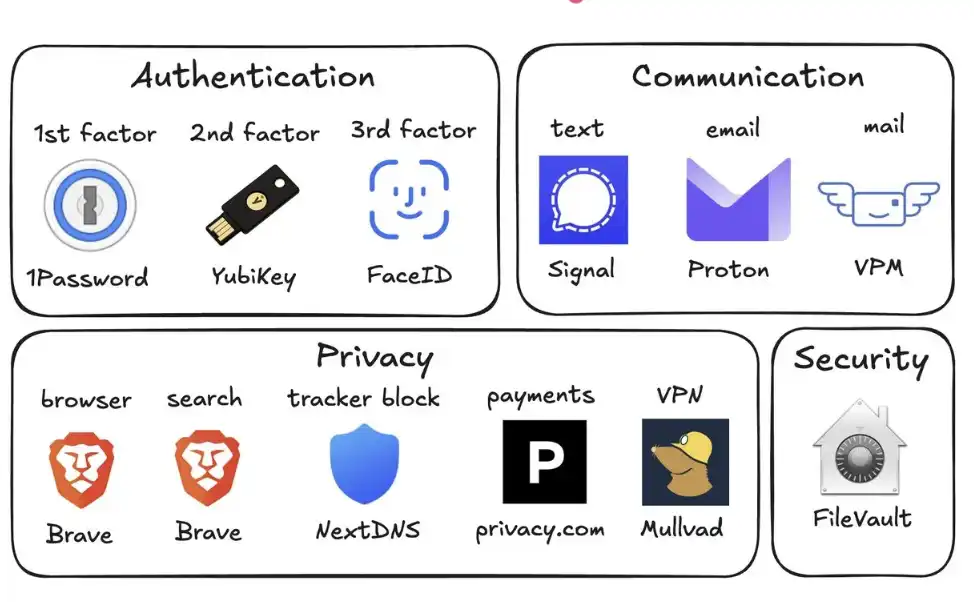
1. Use a Password Manager (e.g., 1Password)
Generate a unique random password for every account you own. Once a service is breached, attackers often use these account passwords for credential stuffing. A password manager can completely mitigate this risk and can even autofill, making it faster in practice than reusing passwords.
2. Set Up Hardware Security Keys (e.g., YubiKey)
This is a physical device that serves as the second factor for logging in. Attackers must "have the physical key" to access your account. In contrast, SMS codes are easily stolen through SIM-swapping attacks (where someone impersonates you to the carrier to transfer your number to their phone).
It is recommended to purchase 2–3 YubiKeys, keep them in different places to prevent being locked out of your accounts if one is lost.
3. Enable Biometrics Everywhere
For example, Face ID, fingerprint recognition, etc., should be enabled in password managers, banking apps, and critical apps. This is the third layer of authentication: "you" yourself. No one can steal your face from a database.
4. Treat Security Questions as Passwords
Questions like "What is your mother's maiden name?" can be found online in 10 seconds. You should generate a random answer and store it in your password manager. Never provide real information.
5. Turn On Disk Encryption
On Mac, it's called FileVault; on Windows, it's BitLocker. If your computer is stolen, encryption ensures that all the thief gets is a "brick" instead of all your data. Enabling this takes only 2 minutes and runs automatically in the background.
6. Reduce Smart Home Devices
Every "smart device" is essentially a connected computer with a microphone. They continuously collect data, connect to the internet frequently, and are often compromised. Your smart home air quality monitor doesn't need to know your exact location. The fewer the devices, the fewer the attack vectors.
7. Use Signal for Communication
Signal provides end-to-end encryption, preventing anyone (including the platform itself, your carrier, eavesdroppers) from reading the content. Regular SMS and even iMessage retain metadata (who, when, frequency of contact). Enable "Disappearing Messages" (e.g., 90 days) to avoid retaining history as a risk.
8. Use Privacy-Focused Browsers (e.g., Brave)
Based on Chromium, compatible with Chrome extensions, offering a nearly identical user experience.
9. Switch Default Search Engine to Brave Search
It has its own index (unlike DuckDuckGo, which relies on Bing). If a search result is unsatisfactory, you can add "!g" to switch to Google. The paid version, around $3 per month, is worthwhile — you become a customer, not the "product being sold."
10. Use Virtual Credit Cards (e.g., Privacy.com)
Generate a unique card number for each merchant and set spending limits. You can even provide random names and addresses. If a merchant is compromised, only the disposable card number is exposed, not your real financial identity.
11. Use a Virtual Mailing Address
Services like Virtual Post Mail will receive your physical mail, scan the contents, and allow you to view them online.
You can decide which items to discard and which to forward. This way, you don't have to give your real home address to various unknown retailers every time you check out online.
12. Do Not Click on Links in Emails
Email addresses are extremely easy to spoof. With the help of AI, today's phishing emails are almost indistinguishable from real ones. Instead of clicking on links, manually enter the website address and log in.
At the same time, disable the automatic image loading feature in your email, as embedded images are often used to track if you've opened the email.
13. Selectively Use a VPN (e.g., Mullvad)
A VPN (Virtual Private Network) can hide your IP address (the unique identifier of your device and location) from services you access. It doesn't need to be on all the time, but make sure to use it when on public Wi-Fi or accessing less trusted services.
14. Set Up DNS-Level Ad Blocking (e.g., NextDNS)
DNS can be thought of as a device's "phone book" for looking up websites. Blocking at this level means ads and trackers are stopped before they even load.
And it works for all apps and browsers on your device.
15. Install Network Monitoring Tools (e.g., Little Snitch)
It shows you which apps on your computer are connecting to the internet, how much data they're sending, and where the data is headed. Any app with an abnormally high "phone home" frequency should raise a red flag and likely be uninstalled.
Currently, Mythos remains solely in the hands of the defense side of Project Glasswing (such as Anthropic, Apple, Google, etc.). However, models with similar capabilities will soon fall into the hands of malicious actors (possibly within 6 months or even sooner).
That's why it's crucial to shore up your security defenses now. Spending 15 minutes to complete these settings can help you avoid a host of serious issues in the future.
Stay secure, and wishing you all the best.
You may also like

1 billion DOTs were minted out of thin air, but the hacker only made 230,000 dollars

After the blockade of the Strait of Hormuz, when will the war end?

Before using Musk's "Western WeChat" X Chat, you need to understand these three questions
The X Chat will be available for download on the App Store this Friday. The media has already covered the feature list, including self-destructing messages, screenshot prevention, 481-person group chats, Grok integration, and registration without a phone number, positioning it as the "Western WeChat." However, there are three questions that have hardly been addressed in any reports.
There is a sentence on X's official help page that is still hanging there: "If malicious insiders or X itself cause encrypted conversations to be exposed through legal processes, both the sender and receiver will be completely unaware."
No. The difference lies in where the keys are stored.
In Signal's end-to-end encryption, the keys never leave your device. X, the court, or any external party does not hold your keys. Signal's servers have nothing to decrypt your messages; even if they were subpoenaed, they could only provide registration timestamps and last connection times, as evidenced by past subpoena records.
X Chat uses the Juicebox protocol. This solution divides the key into three parts, each stored on three servers operated by X. When recovering the key with a PIN code, the system retrieves these three shards from X's servers and recombines them. No matter how complex the PIN code is, X is the actual custodian of the key, not the user.
This is the technical background of the "help page sentence": because the key is on X's servers, X has the ability to respond to legal processes without the user's knowledge. Signal does not have this capability, not because of policy, but because it simply does not have the key.
The following illustration compares the security mechanisms of Signal, WhatsApp, Telegram, and X Chat along six dimensions. X Chat is the only one of the four where the platform holds the key and the only one without Forward Secrecy.
The significance of Forward Secrecy is that even if a key is compromised at a certain point in time, historical messages cannot be decrypted because each message has a unique key. Signal's Double Ratchet protocol automatically updates the key after each message, a mechanism lacking in X Chat.
After analyzing the X Chat architecture in June 2025, Johns Hopkins University cryptology professor Matthew Green commented, "If we judge XChat as an end-to-end encryption scheme, this seems like a pretty game-over type of vulnerability." He later added, "I would not trust this any more than I trust current unencrypted DMs."
From a September 2025 TechCrunch report to being live in April 2026, this architecture saw no changes.
In a February 9, 2026 tweet, Musk pledged to undergo rigorous security tests of X Chat before its launch on X Chat and to open source all the code.
As of the April 17 launch date, no independent third-party audit has been completed, there is no official code repository on GitHub, the App Store's privacy label reveals X Chat collects five or more categories of data including location, contact info, and search history, directly contradicting the marketing claim of "No Ads, No Trackers."
Not continuous monitoring, but a clear access point.
For every message on X Chat, users can long-press and select "Ask Grok." When this button is clicked, the message is delivered to Grok in plaintext, transitioning from encrypted to unencrypted at this stage.
This design is not a vulnerability but a feature. However, X Chat's privacy policy does not state whether this plaintext data will be used for Grok's model training or if Grok will store this conversation content. By actively clicking "Ask Grok," users are voluntarily removing the encryption protection of that message.
There is also a structural issue: How quickly will this button shift from an "optional feature" to a "default habit"? The higher the quality of Grok's replies, the more frequently users will rely on it, leading to an increase in the proportion of messages flowing out of encryption protection. The actual encryption strength of X Chat, in the long run, depends not only on the design of the Juicebox protocol but also on the frequency of user clicks on "Ask Grok."
X Chat's initial release only supports iOS, with the Android version simply stating "coming soon" without a timeline.
In the global smartphone market, Android holds about 73%, while iOS holds about 27% (IDC/Statista, 2025). Of WhatsApp's 3.14 billion monthly active users, 73% are on Android (according to Demand Sage). In India, WhatsApp covers 854 million users, with over 95% Android penetration. In Brazil, there are 148 million users, with 81% on Android, and in Indonesia, there are 112 million users, with 87% on Android.
WhatsApp's dominance in the global communication market is built on Android. Signal, with a monthly active user base of around 85 million, also relies mainly on privacy-conscious users in Android-dominant countries.
X Chat circumvented this battlefield, with two possible interpretations. One is technical debt; X Chat is built with Rust, and achieving cross-platform support is not easy, so prioritizing iOS may be an engineering constraint. The other is a strategic choice; with iOS holding a market share of nearly 55% in the U.S., X's core user base being in the U.S., prioritizing iOS means focusing on their core user base rather than engaging in direct competition with Android-dominated emerging markets and WhatsApp.
These two interpretations are not mutually exclusive, leading to the same result: X Chat's debut saw it willingly forfeit 73% of the global smartphone user base.
This matter has been described by some: X Chat, along with X Money and Grok, forms a trifecta creating a closed-loop data system parallel to the existing infrastructure, similar in concept to the WeChat ecosystem. This assessment is not new, but with X Chat's launch, it's worth revisiting the schematic.
X Chat generates communication metadata, including information on who is talking to whom, for how long, and how frequently. This data flows into X's identity system. Part of the message content goes through the Ask Grok feature and enters Grok's processing chain. Financial transactions are handled by X Money: external public testing was completed in March, opening to the public in April, enabling fiat peer-to-peer transfers via Visa Direct. A senior Fireblocks executive confirmed plans for cryptocurrency payments to go live by the end of the year, holding money transmitter licenses in over 40 U.S. states currently.
Every WeChat feature operates within China's regulatory framework. Musk's system operates within Western regulatory frameworks, but he also serves as the head of the Department of Government Efficiency (DOGE). This is not a WeChat replica; it is a reenactment of the same logic under different political conditions.
The difference is that WeChat has never explicitly claimed to be "end-to-end encrypted" on its main interface, whereas X Chat does. "End-to-end encryption" in user perception means that no one, not even the platform, can see your messages. X Chat's architectural design does not meet this user expectation, but it uses this term.
X Chat consolidates the three data lines of "who this person is, who they are talking to, and where their money comes from and goes to" in one company's hands.
The help page sentence has never been just technical instructions.

Parse Noise's newly launched Beta version, how to "on-chain" this heat?

Is Lobster a Thing of the Past? Unpacking the Hermes Agent Tools that Supercharge Your Throughput to 100x

Declare War on AI? The Doomsday Narrative Behind Ultraman's Residence in Flames

Crypto VCs Are Dead? The Market Extinction Cycle Has Begun

Claude's Journey to Foolishness in Diagrams: The Cost of Thriftiness, or How API Bill Increased 100-Fold

Edge Land Regress: A Rehash Around Maritime Power, Energy, and the Dollar

Arthur Hayes Latest Interview: How Should Retail Investors Navigate the Iran Conflict?

Just now, Sam Altman was attacked again, this time by gunfire

Straits Blockade, Stablecoin Recap | Rewire News Morning Edition

From High Expectations to Controversial Turnaround, Genius Airdrop Triggers Community Backlash

The Xiaomi electric vehicle factory in Beijing's Daxing district has become the new Jerusalem for the American elite

Lean Harness, Fat Skill: The Real Source of 100x AI Productivity

Ultraman is not afraid of his mansion being attacked; he has a fortress.

US-Iran Negotiations Collapse, Bitcoin Faces Battle to Defend $70,000 Level

Reflections and Confusions of a Crypto VC
1 billion DOTs were minted out of thin air, but the hacker only made 230,000 dollars
After the blockade of the Strait of Hormuz, when will the war end?
Before using Musk's "Western WeChat" X Chat, you need to understand these three questions
The X Chat will be available for download on the App Store this Friday. The media has already covered the feature list, including self-destructing messages, screenshot prevention, 481-person group chats, Grok integration, and registration without a phone number, positioning it as the "Western WeChat." However, there are three questions that have hardly been addressed in any reports.
There is a sentence on X's official help page that is still hanging there: "If malicious insiders or X itself cause encrypted conversations to be exposed through legal processes, both the sender and receiver will be completely unaware."
No. The difference lies in where the keys are stored.
In Signal's end-to-end encryption, the keys never leave your device. X, the court, or any external party does not hold your keys. Signal's servers have nothing to decrypt your messages; even if they were subpoenaed, they could only provide registration timestamps and last connection times, as evidenced by past subpoena records.
X Chat uses the Juicebox protocol. This solution divides the key into three parts, each stored on three servers operated by X. When recovering the key with a PIN code, the system retrieves these three shards from X's servers and recombines them. No matter how complex the PIN code is, X is the actual custodian of the key, not the user.
This is the technical background of the "help page sentence": because the key is on X's servers, X has the ability to respond to legal processes without the user's knowledge. Signal does not have this capability, not because of policy, but because it simply does not have the key.
The following illustration compares the security mechanisms of Signal, WhatsApp, Telegram, and X Chat along six dimensions. X Chat is the only one of the four where the platform holds the key and the only one without Forward Secrecy.
The significance of Forward Secrecy is that even if a key is compromised at a certain point in time, historical messages cannot be decrypted because each message has a unique key. Signal's Double Ratchet protocol automatically updates the key after each message, a mechanism lacking in X Chat.
After analyzing the X Chat architecture in June 2025, Johns Hopkins University cryptology professor Matthew Green commented, "If we judge XChat as an end-to-end encryption scheme, this seems like a pretty game-over type of vulnerability." He later added, "I would not trust this any more than I trust current unencrypted DMs."
From a September 2025 TechCrunch report to being live in April 2026, this architecture saw no changes.
In a February 9, 2026 tweet, Musk pledged to undergo rigorous security tests of X Chat before its launch on X Chat and to open source all the code.
As of the April 17 launch date, no independent third-party audit has been completed, there is no official code repository on GitHub, the App Store's privacy label reveals X Chat collects five or more categories of data including location, contact info, and search history, directly contradicting the marketing claim of "No Ads, No Trackers."
Not continuous monitoring, but a clear access point.
For every message on X Chat, users can long-press and select "Ask Grok." When this button is clicked, the message is delivered to Grok in plaintext, transitioning from encrypted to unencrypted at this stage.
This design is not a vulnerability but a feature. However, X Chat's privacy policy does not state whether this plaintext data will be used for Grok's model training or if Grok will store this conversation content. By actively clicking "Ask Grok," users are voluntarily removing the encryption protection of that message.
There is also a structural issue: How quickly will this button shift from an "optional feature" to a "default habit"? The higher the quality of Grok's replies, the more frequently users will rely on it, leading to an increase in the proportion of messages flowing out of encryption protection. The actual encryption strength of X Chat, in the long run, depends not only on the design of the Juicebox protocol but also on the frequency of user clicks on "Ask Grok."
X Chat's initial release only supports iOS, with the Android version simply stating "coming soon" without a timeline.
In the global smartphone market, Android holds about 73%, while iOS holds about 27% (IDC/Statista, 2025). Of WhatsApp's 3.14 billion monthly active users, 73% are on Android (according to Demand Sage). In India, WhatsApp covers 854 million users, with over 95% Android penetration. In Brazil, there are 148 million users, with 81% on Android, and in Indonesia, there are 112 million users, with 87% on Android.
WhatsApp's dominance in the global communication market is built on Android. Signal, with a monthly active user base of around 85 million, also relies mainly on privacy-conscious users in Android-dominant countries.
X Chat circumvented this battlefield, with two possible interpretations. One is technical debt; X Chat is built with Rust, and achieving cross-platform support is not easy, so prioritizing iOS may be an engineering constraint. The other is a strategic choice; with iOS holding a market share of nearly 55% in the U.S., X's core user base being in the U.S., prioritizing iOS means focusing on their core user base rather than engaging in direct competition with Android-dominated emerging markets and WhatsApp.
These two interpretations are not mutually exclusive, leading to the same result: X Chat's debut saw it willingly forfeit 73% of the global smartphone user base.
This matter has been described by some: X Chat, along with X Money and Grok, forms a trifecta creating a closed-loop data system parallel to the existing infrastructure, similar in concept to the WeChat ecosystem. This assessment is not new, but with X Chat's launch, it's worth revisiting the schematic.
X Chat generates communication metadata, including information on who is talking to whom, for how long, and how frequently. This data flows into X's identity system. Part of the message content goes through the Ask Grok feature and enters Grok's processing chain. Financial transactions are handled by X Money: external public testing was completed in March, opening to the public in April, enabling fiat peer-to-peer transfers via Visa Direct. A senior Fireblocks executive confirmed plans for cryptocurrency payments to go live by the end of the year, holding money transmitter licenses in over 40 U.S. states currently.
Every WeChat feature operates within China's regulatory framework. Musk's system operates within Western regulatory frameworks, but he also serves as the head of the Department of Government Efficiency (DOGE). This is not a WeChat replica; it is a reenactment of the same logic under different political conditions.
The difference is that WeChat has never explicitly claimed to be "end-to-end encrypted" on its main interface, whereas X Chat does. "End-to-end encryption" in user perception means that no one, not even the platform, can see your messages. X Chat's architectural design does not meet this user expectation, but it uses this term.
X Chat consolidates the three data lines of "who this person is, who they are talking to, and where their money comes from and goes to" in one company's hands.
The help page sentence has never been just technical instructions.

